By Jeremy Fuchs
Introduction
Successful hacks rarely spell out what’s about to happen.
Instead, hackers rely on deceptive social engineering tactics. The idea is to get you to think you’re doing something legitimate but is, in fact, not.
RELATED: Cloud-based cyberattacks increased by 48% in 2022, as hackers continue to leverage digital transformation
One way to do that is through obfuscation. By hiding the true intent of the email, it may be more likely that a security scanner thinks it is clean, and that an end-user engages with it.
One way to do that is to use something expected–like a picture–and hide the malicious stuff behind it.
In this Attack Brief, Check Point Harmony Email researchers will discuss how hackers hide malicious links within pictures to redirect users to phishing sites.
Attack
In this attack, hackers create magic links that change into the intended destination upon pasting.
- Vector: Email
- Type: Malicious Link
- Techniques: Picture in Picture, Obfuscation
- Target: Any end-user
Email Example
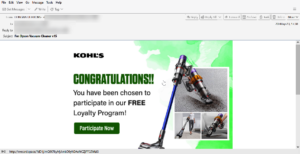
This looks like a fairly standard email. It’s a fake message from Kohl’s, showing that the user has been chosen to participate in their free Loyalty Program. However, the URL has nothing to do with Kohl’s
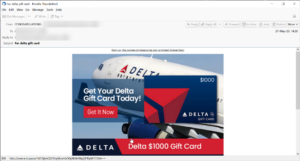
Same thing here. It’s a relatively convincing-looking image of a Delta gift card offer. But again, the URL doesn’t point to Delta.
Both URLs are, in fact, somewhat similar.
When clicking on it, users are redirected to classic credential harvesting pages.
Behind the picture is where the URL lies. Even legitimate pictures from legitimate brands link to a page. Most marketing emails work that way. There will be a nice-looking promotion image, and the link goes to the intended page.
Here, though, the intended page has nothing to do with Delta or Kohl’s and everything to do with stealing your information.
Techniques
Obfuscation is a gift to hackers. It allows them to pull off a magic trick. It works by hiding the true intent of their message.
In this case, it’s a picture. The picture is meant to entice the user to click. Who wouldn’t want a $1,000 Delta Gift Card?
They hope the user will be intrigued enough not to hover over the URL and see that it doesn’t match. An eagle-eyed user would see that and immediately know something is amiss.
And they’re also hoping that the URL filters will be confused too. It’ll look clean if they aren’t scanning within the image. This is a fairly common method. Oftentimes, hackers will happily link a file or image, or QR code to something malicious. Only by using OCR to convert the images to text or parsing QR codes and decoding them can you see the true intention. But many security services don’t or can’t do this.
In this case, the email seems pretty legitimate. Yes, standard things like the sender’s address and the link are off. But it’s a reasonably convincing spoof of Delta and Kohl’s, which legitimizes this otherwise illegitimate act.
That the URL is hidden behind the picture makes things much more challenging.
Best Practices: Guidance and Recommendations
To guard against these attacks, security professionals can do the following:
- Implement security that looks at all URLs and emulates the page behind it
- Leverage URL protection that uses phishing techniques like this one as an indicator of an attack
- Leverage AI-based, anti-phishing software capable of blocking phishing content across the entirety of the productivity suite.
Jeremy Fuchs, is a cybersecurity researcher/analyst at Check Point Software Company