By Oladipupo Adeosun
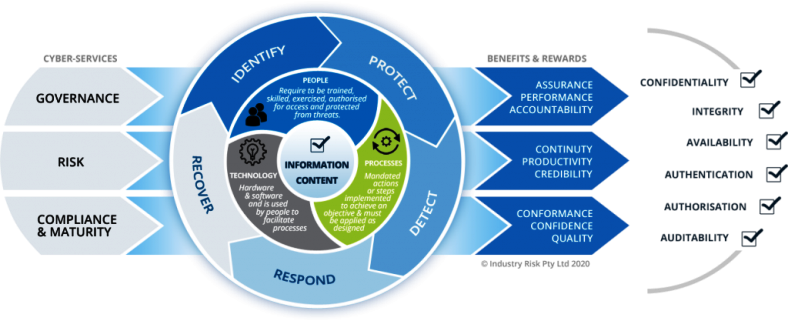
IT governance plays a crucial role in effective cybersecurity risk management within an organization. IT governance involves the processes, structures, and policies that ensure IT resources are aligned with business goals, managed efficiently, and controlled effectively. When integrated with cybersecurity risk management,
RELATED: New IBA report provides first-of-its-kind global perspective on cybersecurity risk governance
IT governance helps establish a framework for making informed decisions, allocating resources, and ensuring that cybersecurity measures are well-defined and consistently applied.
Here’s how IT governance contributes to cybersecurity risk management:
1. Alignment with Business Objectives:
Effective IT governance ensures that cybersecurity strategies are closely aligned with the overall business objectives and risk appetite of the organization. This alignment ensures that cybersecurity measures are not only technically effective but also contribute to the achievement of business goals.
2. Risk Assessment and Management:
IT governance frameworks often include risk assessment and management processes. These processes help identify, assess, and prioritize cybersecurity risks. By integrating cybersecurity risk assessments into IT governance practices, organizations can make informed decisions about resource allocation and risk treatment strategies.
3. Clear Roles and Responsibilities:
IT governance defines roles and responsibilities related to IT and cybersecurity. This clarity helps ensure that cybersecurity responsibilities are properly assigned, understood, and adhered to across the organization. It reduces the likelihood of gaps in security coverage.
4. Policies and Procedures:
IT governance frameworks establish policies and procedures for IT and cybersecurity. These policies provide guidelines for security controls, data protection, access management, incident response, and more. They contribute to a consistent and well-defined approach to managing cybersecurity risks.
5. Decision-Making Processes:
IT governance defines decision-making processes, such as change management and project approval processes. When integrated with cybersecurity, these processes ensure that security considerations are taken into account before implementing new technologies or making changes to existing systems.
6. Resource Allocation:
Cybersecurity requires dedicated resources, including financial, human, and technological. IT governance helps allocate these resources effectively, ensuring that cybersecurity initiatives have the necessary support for implementation and ongoing management.
7. Performance Measurement and Reporting:
IT governance includes mechanisms for measuring and reporting IT performance. By incorporating cybersecurity metrics into these mechanisms, organizations can track the effectiveness of their security measures, identify areas for improvement, and report to stakeholders.
8. Compliance and Regulations:
IT governance frameworks often include compliance controls to adhere to regulations and industry standards. Integrating cybersecurity requirements into these controls helps ensure that the organization remains compliant with relevant cybersecurity regulations.
9. Continual Improvement:
IT governance emphasizes continuous improvement. This approach is essential for cybersecurity risk management as threats and technologies evolve rapidly. Regularly reviewing and updating cybersecurity measures within the IT governance framework ensures that the organization remains resilient to emerging risks.
10. Board Oversight and Accountability:
IT governance often involves reporting to the board of directors or senior management. By including cybersecurity as a part of these reports, organizations ensure that cybersecurity risks and strategies receive the necessary attention at the highest level of the organization.
In essence, IT governance provides the structure, processes, and oversight needed to effectively manage cybersecurity risks. It ensures that cybersecurity is not treated as an isolated technical issue but as an integral part of the organization’s overall risk management strategy. Integrating cybersecurity considerations into IT governance practices creates a holistic approach that supports business objectives while safeguarding critical assets and information.
Oladipupo Adeosun
Head, Information Technology – E-Business (Fintech | Cyber Security | Penetration Tester)