Check Point Research (CPR), the Threat Intelligence arm of Check Point® Software Technologies Ltd. (NASDAQ: CHKP) and a leading provider of cyber security solutions globally, has published its Brand Phishing Report for Q1 2023. The report highlights the brands that were most frequently imitated by cybercriminals in their attempts to steal individuals’ personal information or payment credentials during January, February and March 2023.
RELATED: 60% of e-shop phishing scams exploit Apple’s brand name
Multinational retail giant Walmart topped the ranking last quarter, accounting for 16% of all attempts and climbing from 13th place in Q4 2022. This is due to a significant phishing campaign urging victims to click on a malicious survey link, relating to ‘the supply system collapse’. Meanwhile, DHL held onto second place, appearing in 13% of phishing events, closely followed by Microsoft with 12% during the quarter. Overall, the technology sector was the most imitated industry, followed by shipping and retail.
The latest report also highlights how threat actors are leveraging organizations in the finance sector to steal account details. Bank Raiffeisen made the list for the first to the 8th places. In the Raiffeisen phishing campaign, which accounted for 3.6% of phishing attacks last quarter, recipients were encouraged to click on a malicious link and to ensure the accounts security against any fraudulent activity. Once submitted, those details would then be stolen by the attacker.
“Criminal groups orchestrate phishing campaigns to get as many people to part with their personal data as possible,” said Omer Dembinsky, Data Group Manager at Check Point Software. “In some cases, attacks are designed to obtain account information, as seen with the Raiffeisen campaigns. Others are deployed to steal payment details, which we witnessed with popular streaming service Netflix.”
He added: “The best defense against phishing threats, as ever, is knowledge. Employees should be given appropriate training to spot suspicious traits such as misspelled domains, typos, incorrect dates, and other details that can expose a malicious email or link.”
In a brand phishing attack, criminals try to imitate the official website of a well-known brand by using a similar domain name or URL and a web-page design that resembles the genuine site. The link to the fake website can be sent to targeted individuals by email or text message, a user can be redirected during web browsing, or it may be triggered from a fraudulent mobile application. The fake website often contains a form intended to steal users’ credentials, payment details or other personal information.
Top phishing brands in Q1 2023
Below are the top brands ranked by their overall appearance in brand phishing attempts:
- Walmart (relating to 16% of all phishing attacks globally)
- DHL (13%)
- Microsoft (12%)
- LinkedIn (6%)
- FedEx (4.9%)
- Google (4.8%)
- Netflix (4%)
- Raiffeisen (3.6%)
- PayPal (3.5%)
Raiffeisen Bank Phishing Email – Account Theft Example
This is an example of an attempt to steal a user’s Raiffeisen bank account information through a phishing email. The sender’s name is “Raiffeisen”, but the email address is support@raiffeisen-info[.]com. The email’s subject is “The new SmartToken service is not active” in Romanian (origin:”Noul serviciu SmartToken nu este acti”), and the content claims that the victim needs to activate the “SmartToken“ service to ensure the account’s security against any fraudulent activity. The email contains a malicious link, https://urlz[.]fr/kxnx which the attacker tries to lure the victim into clicking so he could steal his account.
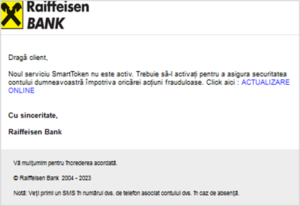
Figure 2: The malicious email which contained the subject
“The new SmartToken service is not active” (origin: “Noul serviciu SmartToken nu este acti”)
Netflix Phishing Scam – Attempts to Steal Payment Details
During the first quarter of 2023, we detected a fraudulent email that utilized Netflix’s branding to deceive individuals. The email, which appeared to originate from “Netflix”, was sent from the webmail address support@bryanadamstribute[.]dk. The subject line of the email was “Uрdаtе rеquіrеd – ассоunt оn hоld“, and the message claimed that the recipient’s Netflix account had been suspended, due to a failure to authorize payment for the next billing cycle. The email provided a link to renew the subscription and requested that the victim enter accurate payment details. However, the link directed users to a malicious website https://oinstitutoisis[.]com/update/login/ with the intention of stealing their payment information.

Figure 3: The malicious email which was sent with the subject
“Uрdаtе rеquіrеd – ассоunt оn hоld”