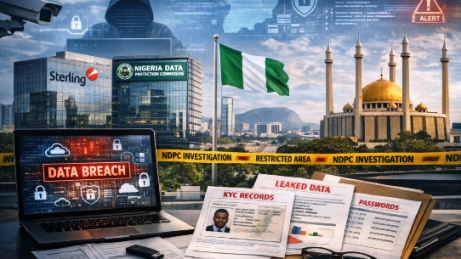
The Nigeria Data Protection Commission (NDPC) has launched a full‑scale investigation into an alleged 3 TB data breach affecting Remita Payment Services Ltd. and Sterling Bank, following alarming claims by a threat actor that vast amounts of sensitive customer and employee data were exfiltrated.
RELATED: NDPC probes alleged data breach involving Remita, Sterling Bank, others in wider digital payments crackdown
What Happened?
According to reports circulating on cybercrime forums, a hacker known as “ByteToBreach” claimed responsibility for infiltrating Sterling Bank’s systems and pivoting into Remita’s infrastructure. The attacker alleges they accessed:
- 3 TB of sensitive data
- 800 GB of KYC documents (passports, driver’s licenses, bank statements)
- Core database exports
- Encryption keys
- Logs and internal backups
- Password hashes
- ~900,000 customer accounts
- 3,000+ employee records (names, BVNs, NINs, transaction histories)
NDPC confirmed that formal Notices of Investigation were served on April 1, 2026, and that both organizations are cooperating.
Who Were the Attackers?
Threat Actor: “ByteToBreach”
- A cybercriminal active on underground forums
- Claims to have exploited a vulnerability in Sterling Bank’s infrastructure
- Allegedly pivoted into Remita’s cloud storage environment
- Some leaked samples appear consistent with the attacker’s past activity, according to analysts (not yet fully verified)
Important: NDPC has not officially confirmed the attacker’s identity.
Who Were the Victims?
Primary Victims
- Sterling Bank customers
- Remita users (including government payment platform users)
- Employees of both organizations
- Potentially millions of Nigerians, given the scale of the alleged dataset
Data Potentially Exposed
- KYC documents (passports, IDs, bank statements)
- BVNs, NINs
- Transaction histories
- Internal system logs
- Database exports
- Encryption keys
- Password hashes
- Cloud storage backups
What Could the Victims (Organizations) Have Done Better?
While the investigation is ongoing, NDPC emphasized the need for stronger technical and organizational safeguards under the Nigeria Data Protection Act (NDP Act 2023).
Likely Areas of Weakness
- Misconfigured cloud storage bucket (explicitly mentioned in the breach claims)
- Insufficient access controls
- Lack of encryption key segregation
- Inadequate monitoring of unusual data exfiltration
- Possible unpatched vulnerability in Sterling Bank’s infrastructure
Best Practices They Should Have Enforced
- Zero‑trust architecture
- Mandatory multi‑factor authentication for all admin accounts
- Continuous vulnerability scanning
- Proper cloud configuration audits
- Encryption key rotation and hardware security modules
- Real‑time anomaly detection
Was There a Fine?
As of the latest reports:
- No fine has yet been issued for this specific incident.
- However, NDPC has a strong enforcement history, including a ₦555.8 million (Nigerian currency) fine against Fidelity Bank for prior data protection violations.
- NDPC warned that any organization using digital payment systems without adequate safeguards will face penalties.
A fine is possible once the investigation concludes.
Lessons Learned
1. Cloud Misconfigurations Are a Major Attack Vector
A misconfigured cloud bucket allegedly exposed 3 TB of data—highlighting how a single oversight can compromise millions.
2. Regulatory Compliance Must Be Continuous
NDPC is increasingly aggressive in enforcing the NDP Act 2023. Organizations must treat compliance as an ongoing process, not a checkbox.
3. Payment Ecosystems Are High‑Value Targets
Fintech and banking platforms hold sensitive identity and financial data—prime targets for attackers.
4. Defense-in-Depth Is Non‑Negotiable
Multiple layers of security (network, application, cloud, identity) are essential to prevent lateral movement like the one described.
5. Users Must Protect Themselves Too
NDPC and security experts advise customers to:
- Change passwords and PINs
- Enable 2FA
- Monitor bank statements
Conclusion
The alleged Remita–Sterling Bank breach is one of the largest in Nigeria’s financial history, with claims of 3 TB of highly sensitive data stolen by a threat actor known as “ByteToBreach.” While the full extent is still under investigation, the incident underscores the urgent need for robust cybersecurity, strict compliance with the NDP Act, and proactive risk management across Nigeria’s digital payment ecosystem.
NDPC’s ongoing probe signals a clear message: Data protection is no longer optional—it’s a legal and operational imperative.

Claudia Salajan, Cybersecurity Compliance & Governance Expert and GDPR Consultant and Auditor